Are you looking for a way to use the Social Engineer Toolkit in Kali?
Social engineering attacks have become a significant threat to personal and organizational security. Understanding and defending against these attacks is vital. This guide focuses on the Social Engineering Toolkit (SET) – an essential tool for cyber security professionals, ethical hackers, and security enthusiasts alike.
Join us as we discuss three different ways to use this software. As you read on, you’ll discover the versatility of SET, learn how to leverage its features, and gain valuable insights into the ever-growing world of social engineering attacks.
We will show you how to use the infectious media generator to create a malicious EXE. Next, we will show you how to set up an individual phishing attack, and lastly, we will show you how to use the Social Engineer Toolkit to clone a legitimate website and harvest credentials.
What Is the Social Engineer Toolkit?
Before diving into the Social Engineering Toolkit, let’s discuss what social engineering is.
Social Engineering
Social engineering is a psychological tactic that tricks people into taking certain actions or revealing sensitive information. It relies on exploiting human emotions, trust, and curiosity rather than using technical methods to gain unauthorized access to confidential data.
In simple terms, social engineering is like a con artist’s game, where the attacker manipulates the target’s feelings and trust to get what they want.
By understanding and manipulating human behavior, these attackers can deceive their victims into disclosing their details, like passwords or financial information, or performing actions that compromise security.
The Social Engineer Toolkit
The Social Engineer Toolkit (SET), written in Python, is a powerful collection of tools designed for social engineering. Penetration testers or Red Team members often use it to test an organization’s security by simulating social engineering attacks on employees.
Developed by TrustedSec and available on GitHub, SET comes pre-installed on Kali Linux, making it a readily accessible resource for cyber security professionals.
Need guidance on installing Kali on VMware or VirtualBox? Check out our easy-to-follow guides to get started with your virtual lab setup!
SET offers many attack vectors, such as spear phishing, malicious payloads, infectious media generation, and website cloning. These attacks leverage the inherent human vulnerabilities of most security systems, making them potent and challenging to defend against.
Getting Started with Social Engineer Toolkit
Having discussed what social engineer toolkit is, let’s move on and discuss the setup and the numerous options it has.
Warning
The information provided in this blog, including using the Social-Engineer Toolkit (SET), is for educational purposes. We urge you to apply the techniques and knowledge shared here only with explicit permission from the relevant parties. Engaging in unauthorized hacking activities is unethical and illegal. We encourage you to practice responsible and ethical hacking.
Startup
The Social Engineer Toolkit already comes pre-installed in Kali. To start SET, simply head to your terminal and type: sudo setoolkit
You will be asked to read the terms and conditions before continuing.

Options
Once SET launches, you’ll be presented with a menu of options. This article will focus on option one: Social-Engineering Attacks, which offers a variety of attack vectors. Here is an overview of the options available in this category:
1) Social-Engineering Attacks: This option focuses on various social engineering attack vectors, including spear phishing, website attacks, infectious media generation, and credential harvesting. It allows users to simulate and test various human-centered attack scenarios.
2) Penetration Testing (Fast-Track): Fast-Track is a collection of testing tools and scripts designed to rapidly deploy and exploit security vulnerabilities. It helps automate various aspects of penetration testing and speeds up the process of discovering and exploiting vulnerabilities
3) Third Party Modules: This option provides integration with external tools and modules developed by the security community. These modules extend SET’s functionality and can offer additional attack vectors, exploits, and payloads for use within the toolkit.
4) Update the Social-Engineer Toolkit: This option allows you to update SET to the latest version, ensuring you have the most recent features, bug fixes, and improvements. Regular updates are essential to maintaining an effective and reliable toolkit.
5) Update SET configuration: This option lets you modify the SET configuration file.
6) Help, Credits, and About: This option provides access to the help documentation, credits to the developers and contributors, and general information about the Social Engineer Toolkit. It is a useful resource for understanding the toolkit’s functionality, getting assistance, and learning about its development history.
Infectious Media Generator
The Infectious Media Generator in SET allows you to create malicious files, such as PDFs and EXEs, that can trigger a reverse Meterpreter shell when opened. This section will guide you through the process of creating a malicious EXE.

SET has many options for malicious payloads, but they may be limited depending on the software and operating system versions the target is using.
Setup
- From the SET main menu, select one “Social-Engineering Attacks.”
- Choose three “Infectious Media Generator.”

There are two options inside the “Infectious Media Generator,” “File-Format Exploits,” and “Standard Metasploit Executable.”
File-Format Exploits: This attack vector exploits vulnerabilities in popular formats like PDFs, Microsoft Office documents, and image files. Attackers craft malicious files containing embedded payloads that, when opened by unsuspecting users, exploit these vulnerabilities to gain unauthorized access to their systems.
The primary advantage of this approach is its stealthiness, as the malicious files often appear legitimate and are less likely to raise suspicion. Moreover, users perceive these file formats as harmless, making them more likely to be opened.
These are dependent on the OS version of the target system.
Standard Metasploit Executable: Using the Metasploit Framework, this attack vector involves creating a standalone executable containing a malicious payload.
When a user runs the executable, the payload is executed, and the attacker gains control over the target system. This approach is more straightforward than File-Format Exploits, as it doesn’t rely on exploiting specific vulnerabilities in file formats.
However, it may also be more conspicuous, as users are generally more cautious when running unfamiliar executables. A successful attack using this vector often relies on strong social engineering techniques to convince the target to run the executable, such as disguising it as a software update, a useful utility, or a desirable file.
Next, you will be asked which format you would like to use. We will be selecting option two.

You will be asked to select the reverse shell you want to use. For this option, choose two, which is the Windows Meterpreter Reverse TCP shell. Enter the IP address and port for your listener.

The Social Engineering Toolkit will now create the malicious exe file, call it payload.exe, and save it to the /root/.set directory.

You can now rename the file to something else if you want. An attacker might change the name to something that will entice a victim to click on it, such as an update for an application.

Start the multi-handler in metasploit using the same IP and port you chose above and type run.

The user must click on the malicious file to initiate the reverse shell.

Once the user clicks the file, you should have a reverse meterpreter shell to the target.

In search of a reverse shell cheat sheet? We’ve got you covered in our detailed post. Check it out now!
Phishing Attacks
Phishing is a widely-used social engineering attack that aims to deceive users into revealing sensitive information, such as login credentials, financial details, or personally identifiable information.
By manipulating users into believing they are interacting with a legitimate source, attackers can trick them into clicking on malicious links, downloading malware-infected files, or divulging confidential information.
You can use Gmail, Hotmail, Yahoo, or an email address from your domain to perform a phishing attack with SET. Gmail is the default option and the one we will be using. To change between Gmail, Hotmail, or Yahoo, you must edit the /etc/setoolkit/set.config file.

Mass Mailer
With the mass mailer option in SET, you can create a phishing email and send it to the target. SET allows for both individual phishing and mass mailing attacks, with the latter targeting multiple victims simultaneously.
In this walkthrough, we will show you the individual attack and how we can include a malicious link to a cloned site we will be creating in our next section. The mass mailer attack is similar; the only difference being you can use a list of emails instead of a single address.
You will need to use an App password to use a Gmail account. App passwords let you sign in to your Google Account from apps on devices that don’t support 2-Step Verification.
Here is a great article on setting up App passwords in your Google account.
Google is removing this option for new accounts and has plans to remove it from all accounts in the future, so be aware that using your Gmail account may not work, and you may need to use an email from a domain you own instead.
You will need an SMTP open relay to use an email attached to your domain. For this scenario, we recommend using SMTP2GO, where you can send up to a thousand emails at no cost.
Phishing Campaign
Let’s walk you through setting up the phishing campaign using a Gmail address to send an email with a malicious link.
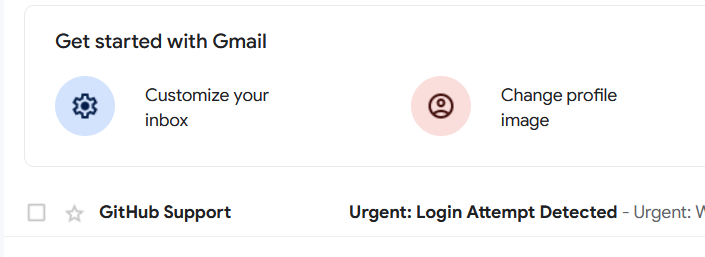
We will email the target pretending to be GitHub support and ask the user to click the link. The link will be to a cloned site we will host on our server.
From the main menu, choose option one, “Social Engineering Attacks,” then choose option five, “Mass Mailer Attack,” and finally select “E-mail Attack Single Email Address.”

You will be asked to input the target and sender email. Let’s walk through each prompt.
- Send email to: This is the email of the target.
- Next, you can use a Gmail account or one from your server.
- Your Gmail account: The account you want to send the email from.
- The FROM NAME the user will see: The from name you want to be displayed.
- Flag this message(s) as high priority: Whether you want it to be flagged as high priority.
- Do you want to attach a file: Yes or No
- Do you want to attach an inline file: Yes or No
- E-mail Subject: The subject line for the email.
- Send the message as HTML or plain text: Choose how you want to send the email.
- Enter the body of the message: Enter the actual email text here. Once you have finished writing the email, type END and hit enter.
SET will tell you when it has finished sending the emails.

Once the email has been sent, your target should receive it in their inbox.

If you want to send an email from your server, the setup in SET is similar. You need the SMTP server and port number from your server. For SMTP2GO, that would be mail.smtp2go.com and port 2525. You need a username and password, which can be set up in SMTP2GO.
An attacker may often use “typosquatting” or “URL hijacking” to register domain names similar to legitimate ones. Doing so allows them to use a more convincing email address to send out phishing emails.

Now, let’s look at setting up a cloned Github login page where we will direct our target and harvest their credentials.
Website Cloning and Credential Harvesting
Website cloning and credential harvesting are two essential techniques in the arsenal of social engineers. These techniques involve creating a replica of a legitimate website and tricking users into entering their sensitive information on the fake website, such as usernames and passwords.
This information can then be used for various malicious activities, including unauthorized access to user accounts, identity theft, or even corporate espionage.

Clone Site
Before setting up a cloned site in SET, you need to enable the Apache web server in the SET configuration file located at /etc/setoolkit/set.config. Change the line APACHE_SERVER=OFF to APACHE_SERVER=ON, save the file, and restart SET to apply the changes.

To use the Site Cloner in SET, follow these steps:
- Launch SET by running setoolkit in the terminal.
- Select option one, which is Social-Engineering Attacks.
- Choose option two, Website Attack Vectors.
- Select option three, Credential Harvester Attack Method.
- Choose option two, Site Cloner.

- Enter the IP address of the machine running SET, which will be used as the redirect IP for captured credentials.
- Input the URL of the target website you want to clone (e.g., https://bit.ly/3BxoUiD).

SET will now clone the website and host it on your machine, with a phishing page to capture user credentials.
For this to work effectively, you need to clone a site that has the username and password fields on the same page.

Credential Harvesting
When users visit the cloned website and enter their login information, the credentials will be captured and sent to the attacker’s machine. This information can then be used to gain unauthorized access to the user’s account on a legitimate website.
The user will then be redirected to the actual login page of the service.

If we head back to our terminal in Kali, we should see the credentials come through.

To make the cloned website more convincing, attackers often employ tactics like typosquatting (registering domains with similar names to the target site), such as amzon.com (instead of amazon.com), or using the target site’s name as a subdomain of another legitimate site they control (amazon.myfakesite.com).
These techniques help create a sense of credibility for the fake website, increasing the chances of successfully tricking users into revealing their credentials.
It’s important to note that tools like SET can quickly deploy cloned websites on cloud platforms like AWS, complete with public URLs, making it even easier for attackers to create convincing phishing campaigns.
Always remember to use these tools and techniques for educational purposes and in authorized penetration testing engagements only. Ethical hacking is about understanding and improving security, not exploiting it for malicious purposes.
Conclusion
Throughout this guide, we have explored the powerful capabilities of the Social Engineer Toolkit (SET) in conducting various social engineering attacks. We’ve delved into the Infectious Media Generator, creating malicious payloads that can compromise systems upon execution.
We’ve also discussed phishing attacks and how to send a malicious link in an email. Finally, we examined website cloning and credential harvesting, highlighting the importance of awareness and vigilance regarding online security.
However, it is crucial to remember that SET is capable of much more than what we’ve covered in this guide. Other attack vectors, penetration testing modules, and third-party integrations make SET indispensable for ethical hackers, security researchers, and penetration testers.
As we continue to emphasize, the knowledge and techniques shared in this guide should only be used for educational purposes or authorized security assessments.
The Social Engineer Toolkit is a versatile and powerful suite of tools that can significantly aid security professionals in understanding and mitigating the risks associated with social engineering attacks. By becoming familiar with these techniques and tools, you’ll be better equipped to protect yourself, your organization, and your users from falling victim to the ever-evolving landscape of cyber security threats.
Why not explore some of our fantastic courses that can help you expand your knowledge in social engineering?
from StationX https://bit.ly/3pRfUlO
via IFTTT



No comments:
Post a Comment