- Attackers are abusing normal features of legitimate web sites to transmit spam, such as the traditional method of verifying the creation of a new account.
- This web infrastructure and its associated email infrastructure is otherwise used for legitimate purposes, which makes blocking these messages more difficult for defenders.
- The breadth of different sources of spam suggests that the attackers have automated the process of initially identifying web infrastructure vulnerable to abuse. However, the complexity of executing each individual attack suggests more human involvement.
- Attackers are also testing credentials obtained from data breaches by credential stuffing IMAP and SMTP accounts.

Spammers are always looking for creative ways to bypass spam filters. As a spammer, one of the problems with creating your own architecture to deliver mail is that, once the spam starts flowing, these sources (IPs/domains) can be blocked. Spam can more easily find its way into the inbox if it is delivered from an unexpected or legitimate source. Realizing this, many spammers have elected to attack web pages and mail servers of legitimate organizations, so they may use these “pirated” resources to send unsolicited email.
There are many ways spammers accomplish this task: One is to abuse web pages connected to backend SMTP infrastructure, and another uses breached email/password credentials to try and log into email accounts they can use to send spam. Cisco Talos has new research that explores both styles of attack and delves into some of the tools used by spammers.
Web form abuse
The HTML <form> tag was released with HTML version 2.0, nearly 30 years ago. Since then, spammers have found creative ways to abuse web forms. The lack of proper input validation left many of these forms open to manipulation by attackers. Over time, these HTML form attacks became more sophisticated, sometimes employing cross-site scripting or SQL injection. Many administrators learned the hard way that their forms were vulnerable and were forced to harden their forms as a result. However, spammers are a persistent bunch, and they look for anything they can use to facilitate malicious activities. Creative spammers have realized that *any* web form that triggers an email back to the user can be abused.
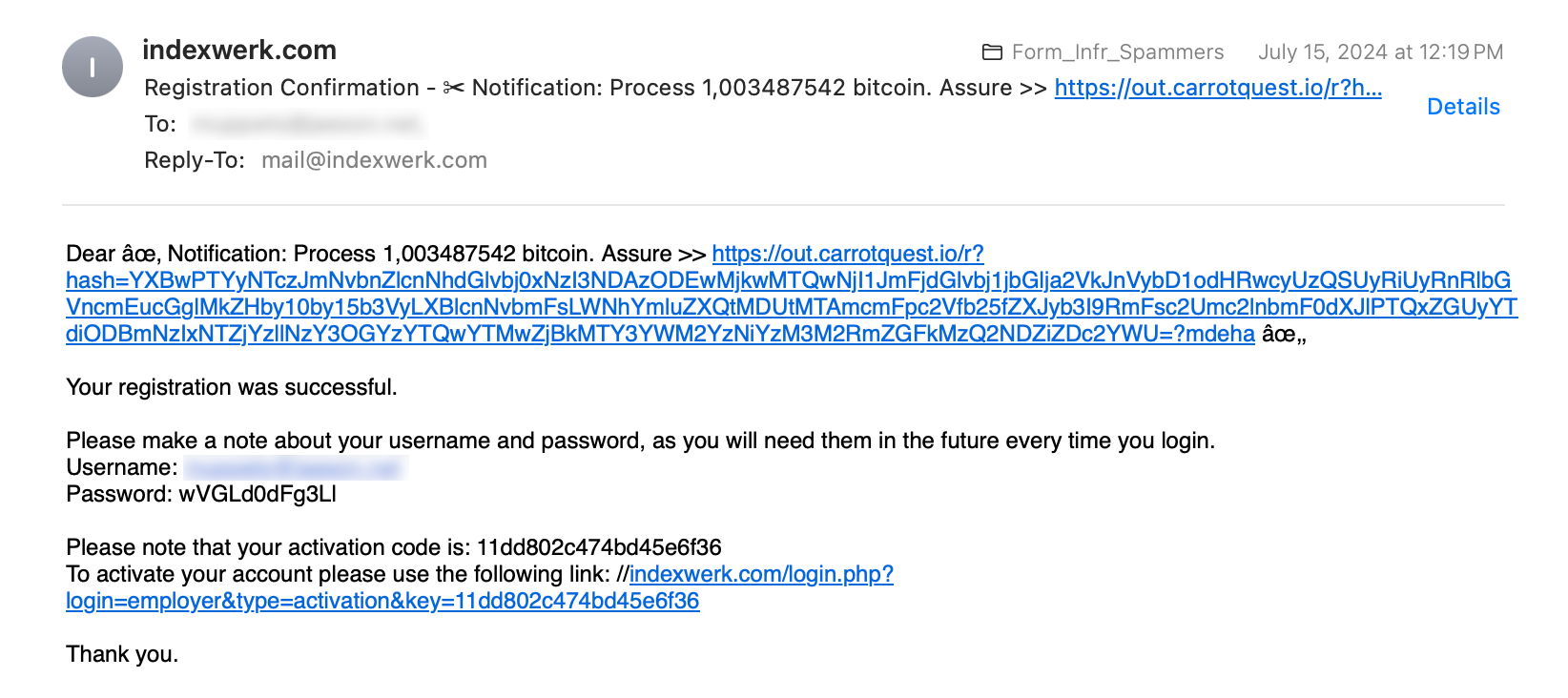
Online account registration
Many websites allow users to sign up for an account and log in to access specific features or content. Typically, upon successful user registration, an email is triggered back to the user to confirm the account. In this case, the spammers have overloaded the name field with text and a link, which is unfortunately not validated or sanitized in any way. The resulting email back to the victim contains the spammer’s link.
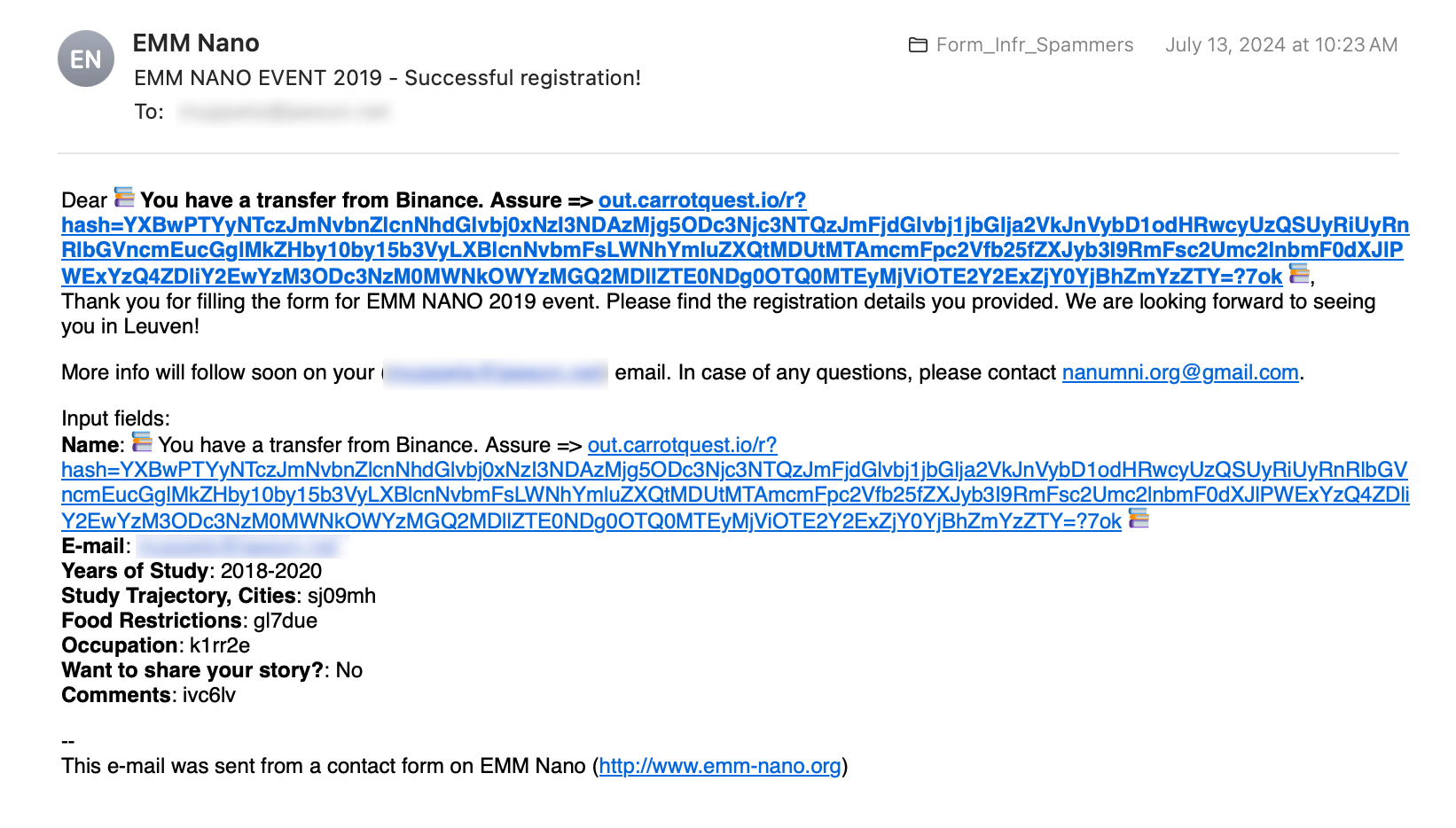
Event signup
Like account registration, many websites let users register to participate in an event. Again, poor input validation and sanitization is prevalent on many of these sites, allowing the spammers to overload the name field with text and URLs.
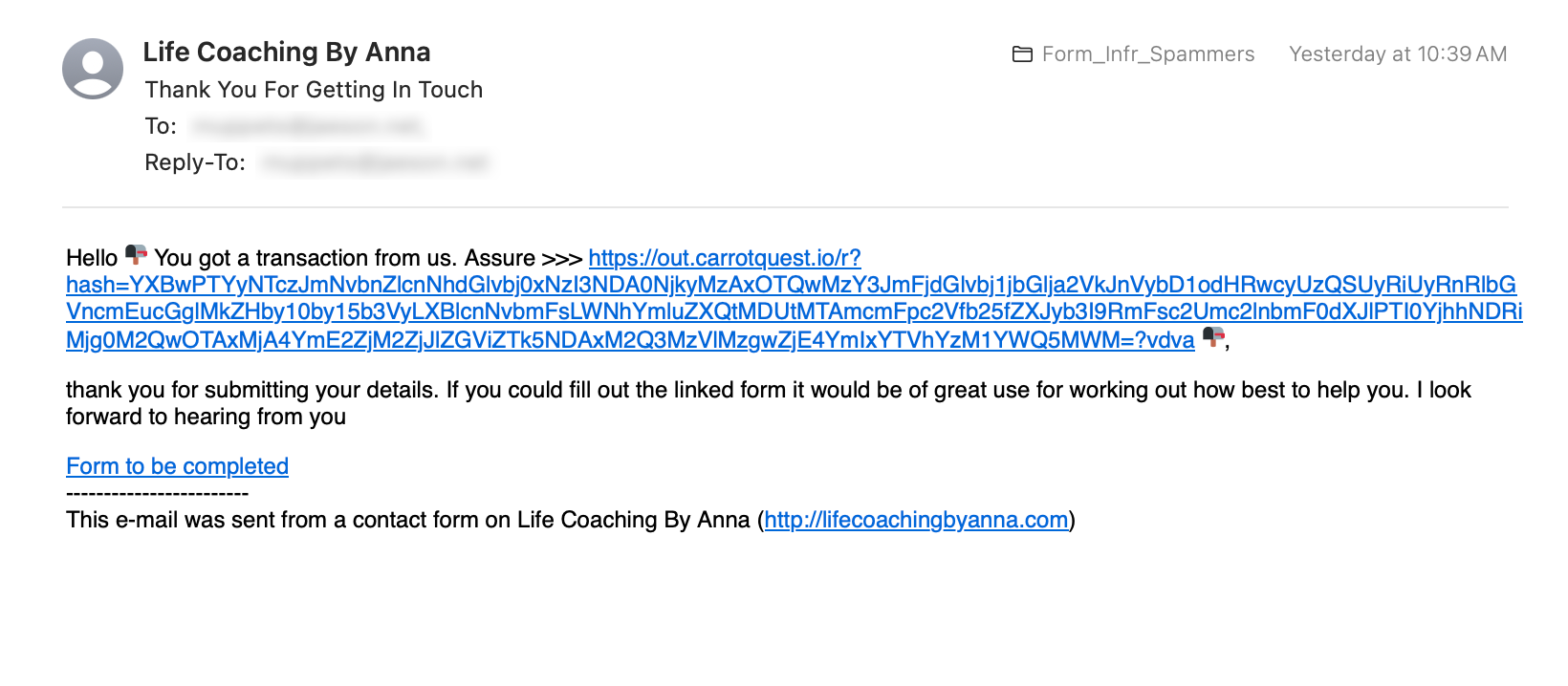
Contact form
Contact forms sometimes send users a copy of their form responses. This could be a checkbox on the form or an automatic reply. Again, the spammers rely on poor input validation and sanitization to transmit text and URLs to the victim.
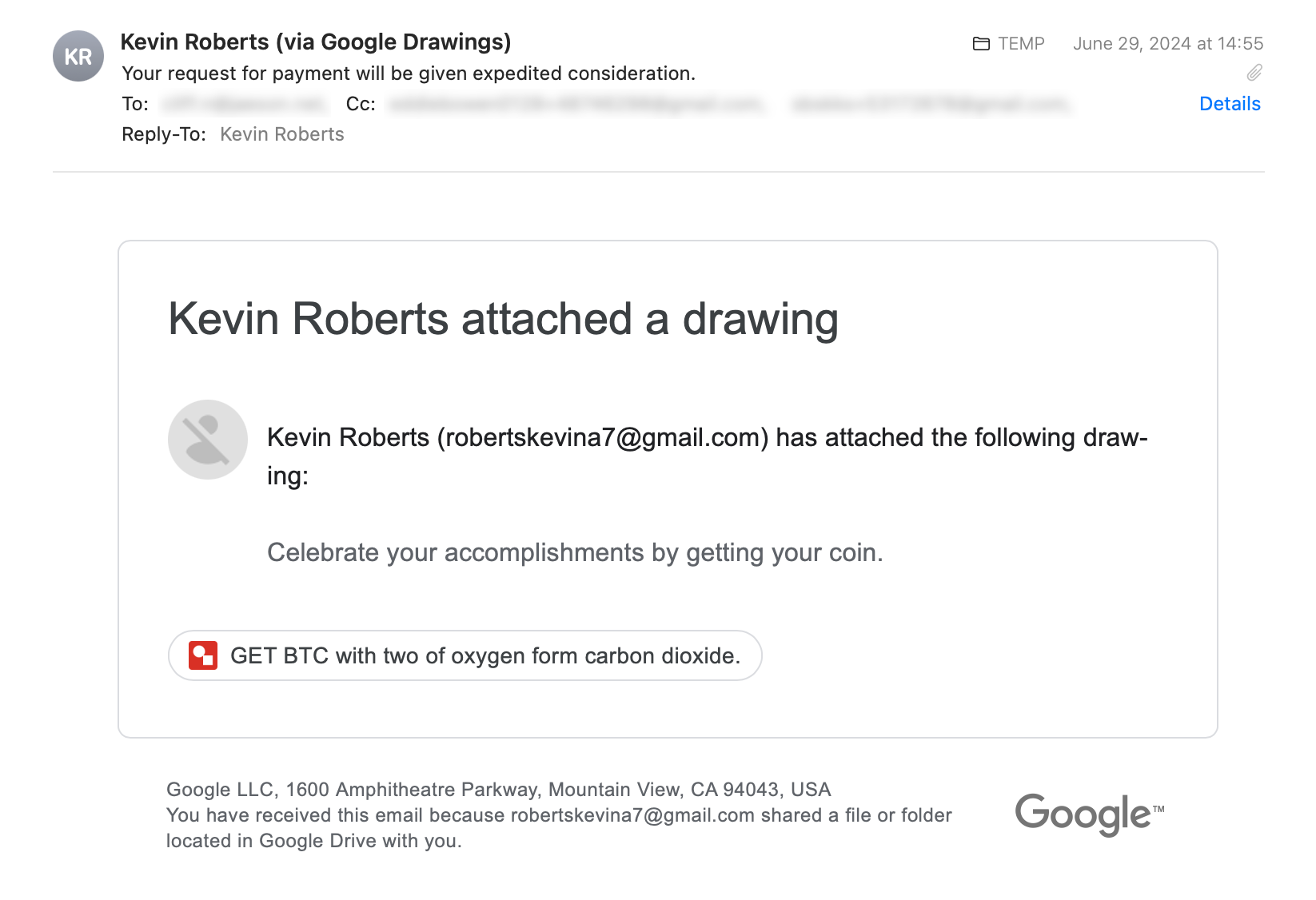
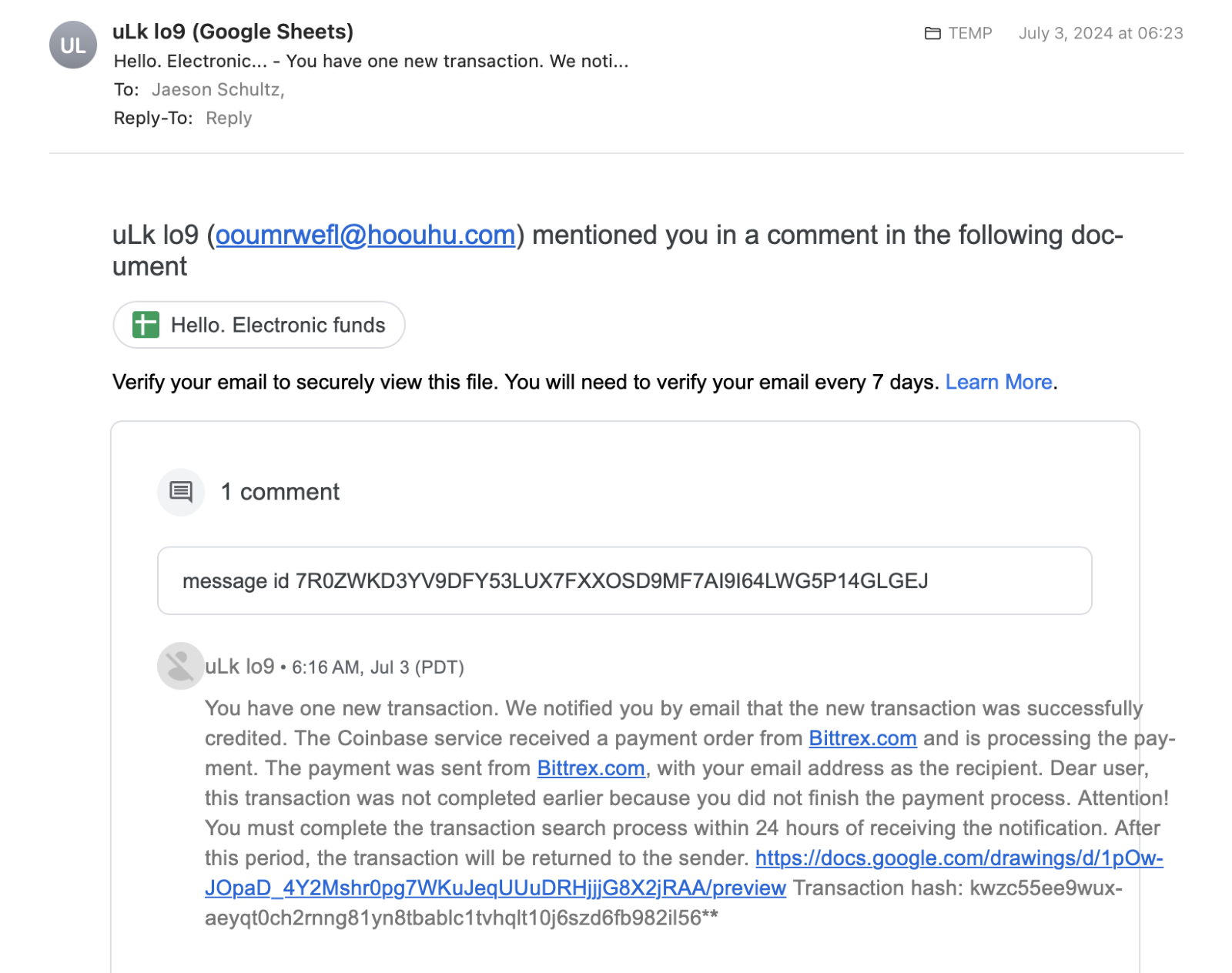
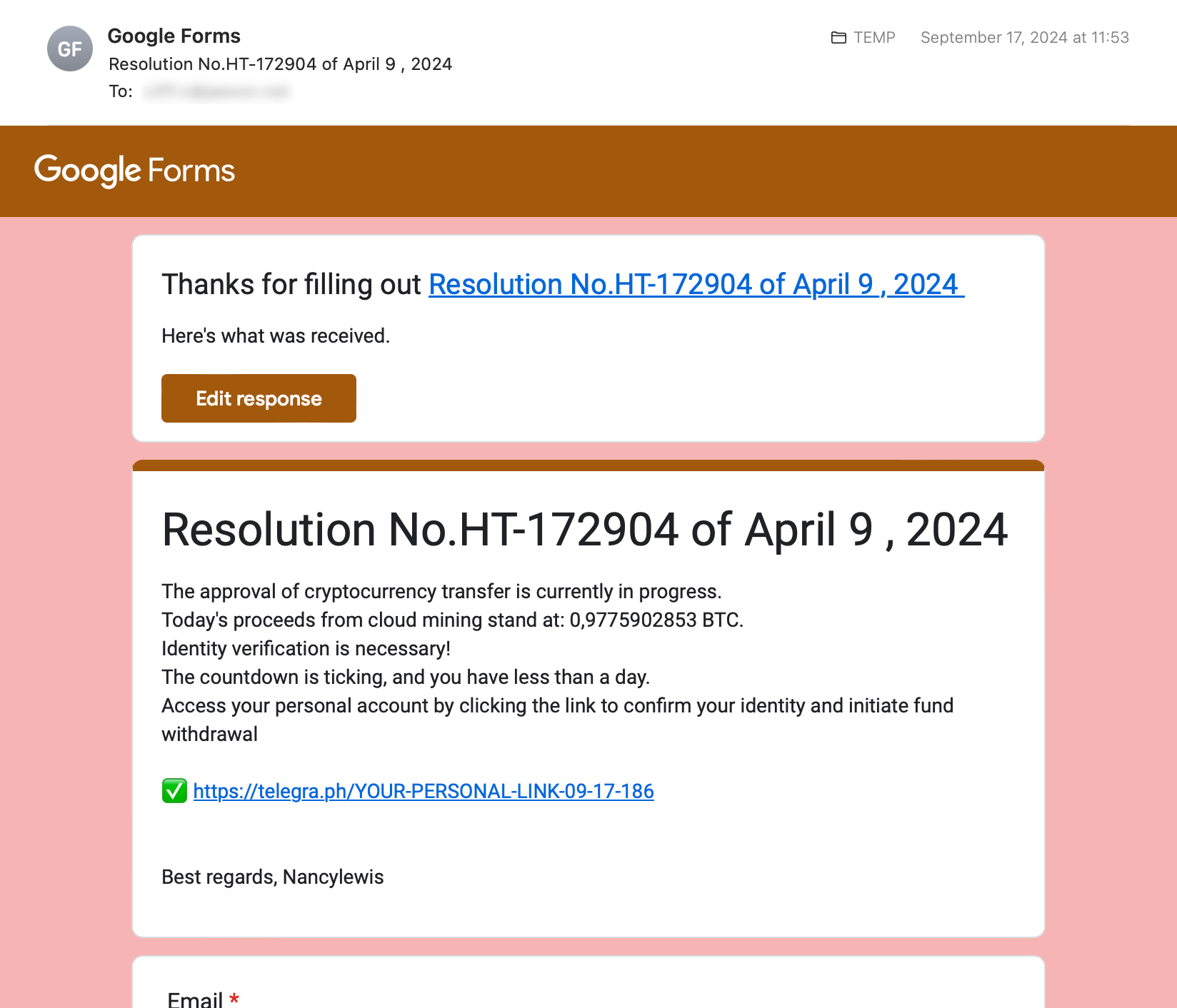
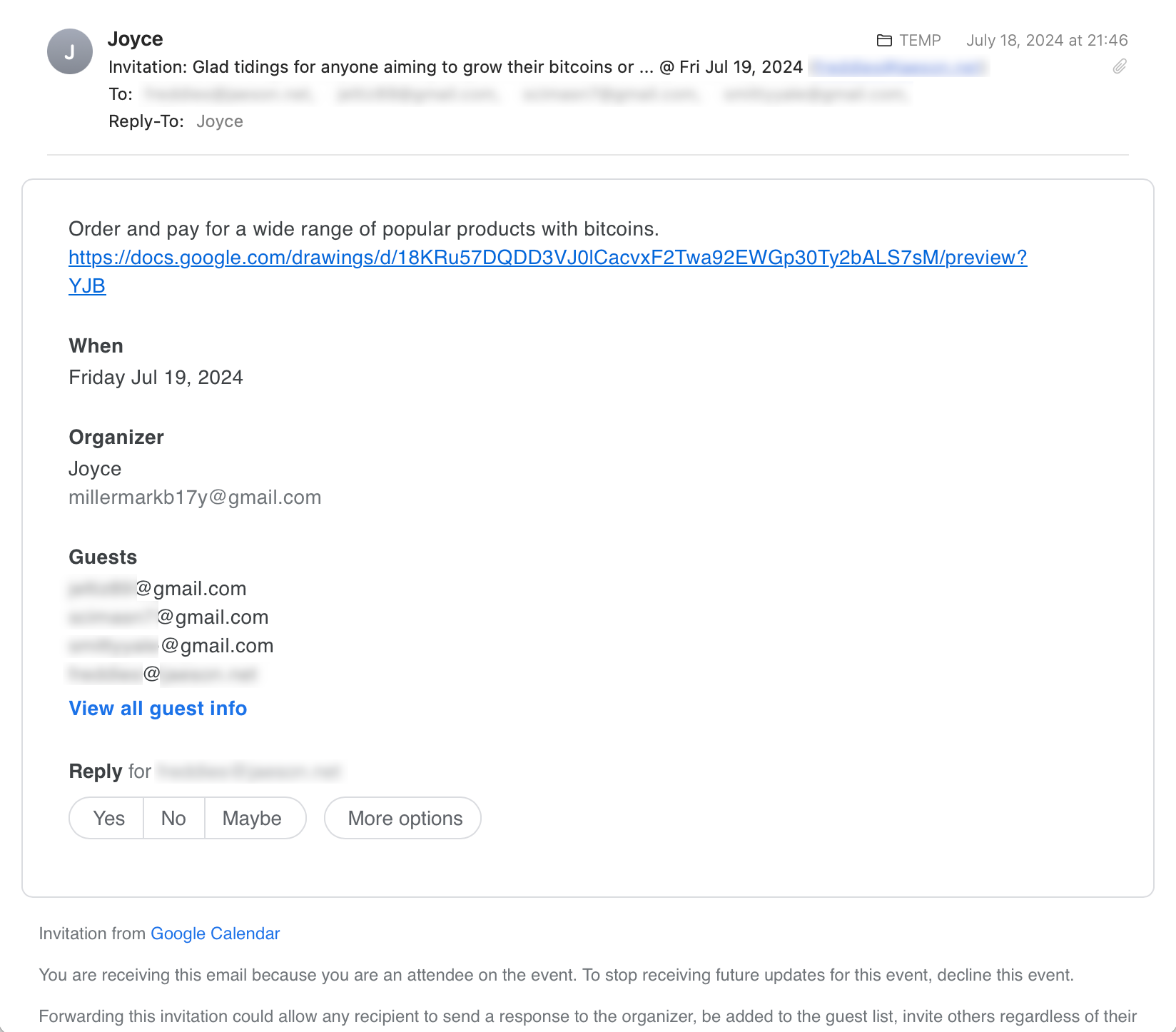
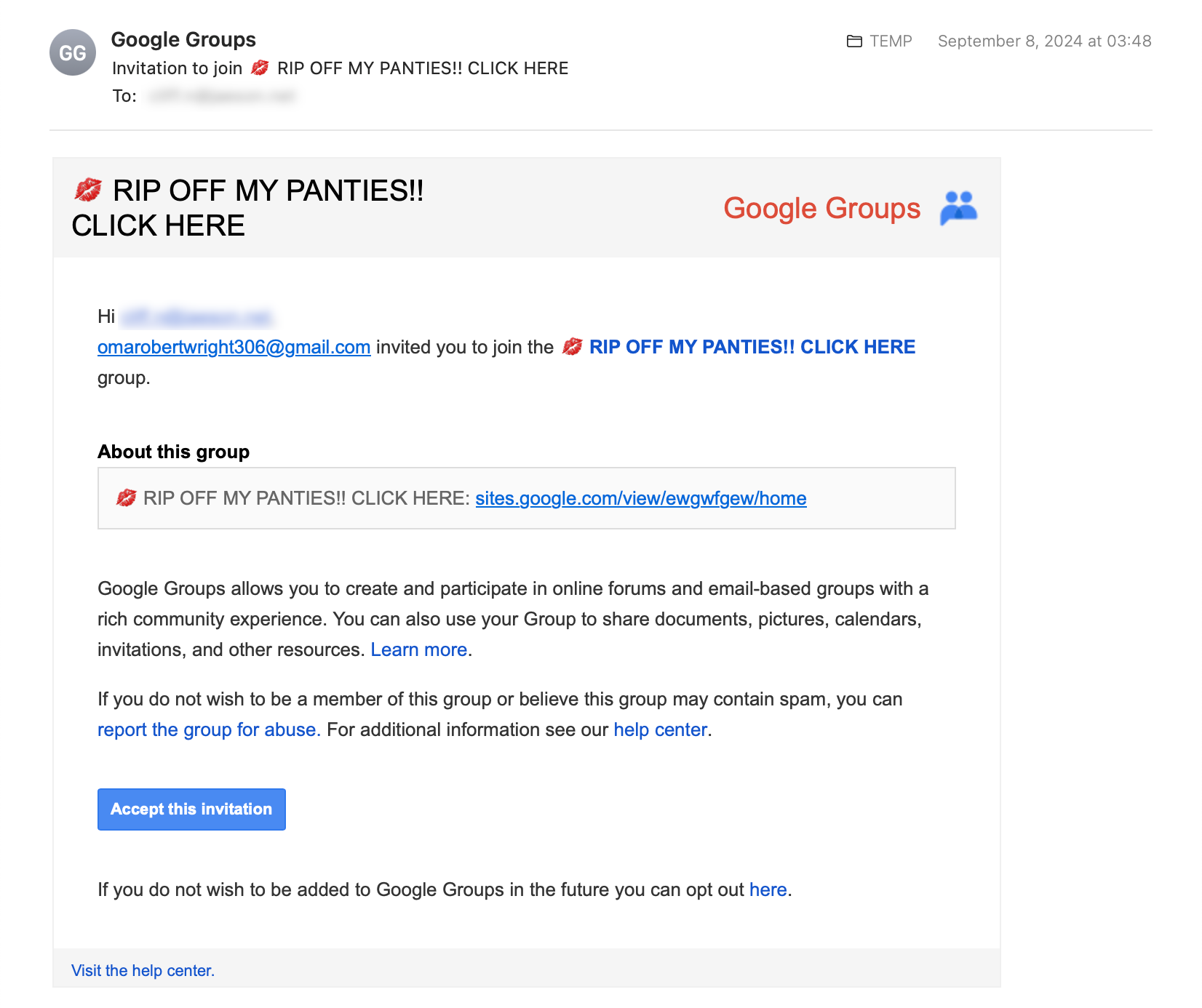
Google Quizzes, Calendar, Groups and other apps
Talos previously reported on spammers abusing Google Quizzes. But that is not the only Google software that spammers have been abusing. Google Drawings, Sheets, Forms, Calendar and Groups all contain similar vulnerabilities that allow spammers to send unsolicited emails to victims. Additionally, by using a variety of Google applications, and ones that are located in different countries, they can largely avoid detection by Google.
These messages from Google require some significant pre-attack setup. For example, to send spam from Google Quizzes, the attackers must set up a quiz and configure it correctly, then they must fill out the quiz, masquerading as the victim. Then, the attackers must log back into the Google Quiz they created to “grade” the results and send the quiz score email back to the victim. This suggests a significant human interaction on the part of the spammers.
Unfortunately for defenders, there is very little we can do to defend against such spam messages. Most of the emails sent by these contact forms are legitimate, so the malicious email blends in with the otherwise legitimate traffic. However, on the positive side, some of the extra content in the emails gives away that the message is not legitimate.
SMTP server credential stuffing
Have you ever wondered what cyber criminals do with all the information they’ve obtained in a data breach? If the stolen dataset contains email address usernames and passwords, then it is quite probable that those same credentials will work in other places. Trying the same set of credentials at other sites is known as “credential stuffing.”
One of the main ways cybercriminals leverage stolen credentials is attempting to access the victim’s email. POP/IMAP servers are often juicy targets, because if an attacker can access a person’s email inbox, then they can find other accounts used by the victim, account usernames/passwords, cryptocurrency wallet keys or perhaps other lucrative, sensitive personal information. Attackers can also leverage access to the victim’s inbox to receive email-based multifactor authentication codes or password resets.
One of the other, lesser-known ways attackers leverage stolen credentials is on the outbound side of the victim’s mailbox. If an attacker can log into the outbound smtp server as the victim, they can send out email using the victim’s email server. This provides the cybercriminal with a legitimate mail server and domain which are not likely blocked by various spam real-time blackhole lists (RBLs).
How do cybercriminals locate mailboxes that have working credentials? Typically, the attacker will set up a personal mailbox somewhere (Yahoo, Gmail, etc.) and then send themselves test messages using the stolen credentials at the outbound SMTP server matching the email address’ domain. Some criminals have turned this into an online business by finding working SMTP server credentials and selling them to others.
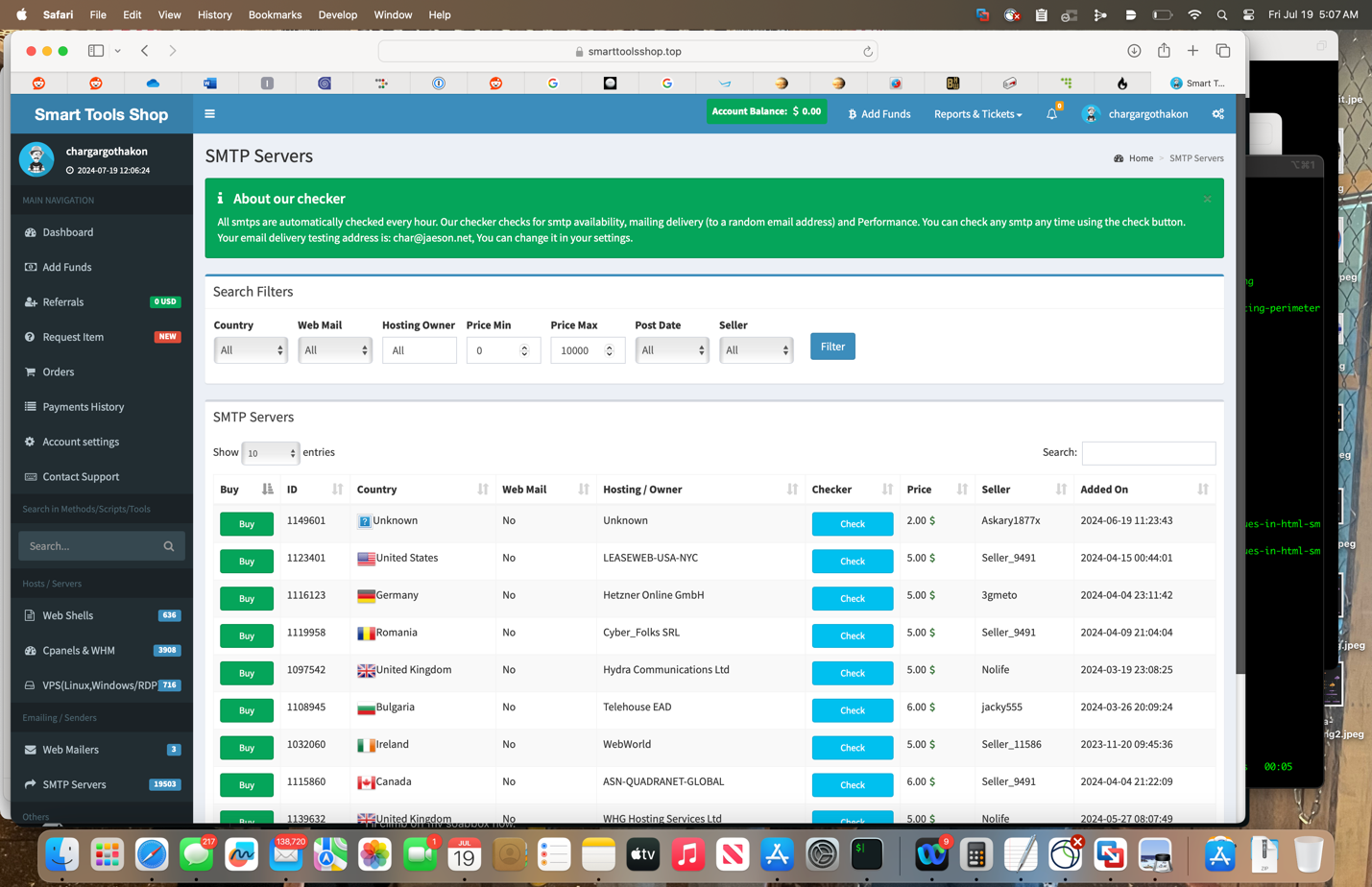
There are also open-source tools used for these sorts of activities. Among the tools Talos sees most frequently are MadCat and MailRip, both of which are available to download and run on GitHub.

MadCat is an open-source SMTP tool that includes credential-stuffing capabilities. The test emails can be recognized from the Subject header: “Subject: You get a new smtp”. Among some of MadCat’s advertised features is the ability to skip emails hosted by known security vendors such as Cisco. This feature is implemented rather poorly, however, because the code used to skip “dangerous emails” is simply a regular expression with words like “cisco,” “cloudflare,” “proofpoint,” etc., as if spam traps implemented by security organizations are all run out of the main corporate domain name (Spoiler alert: they are not).
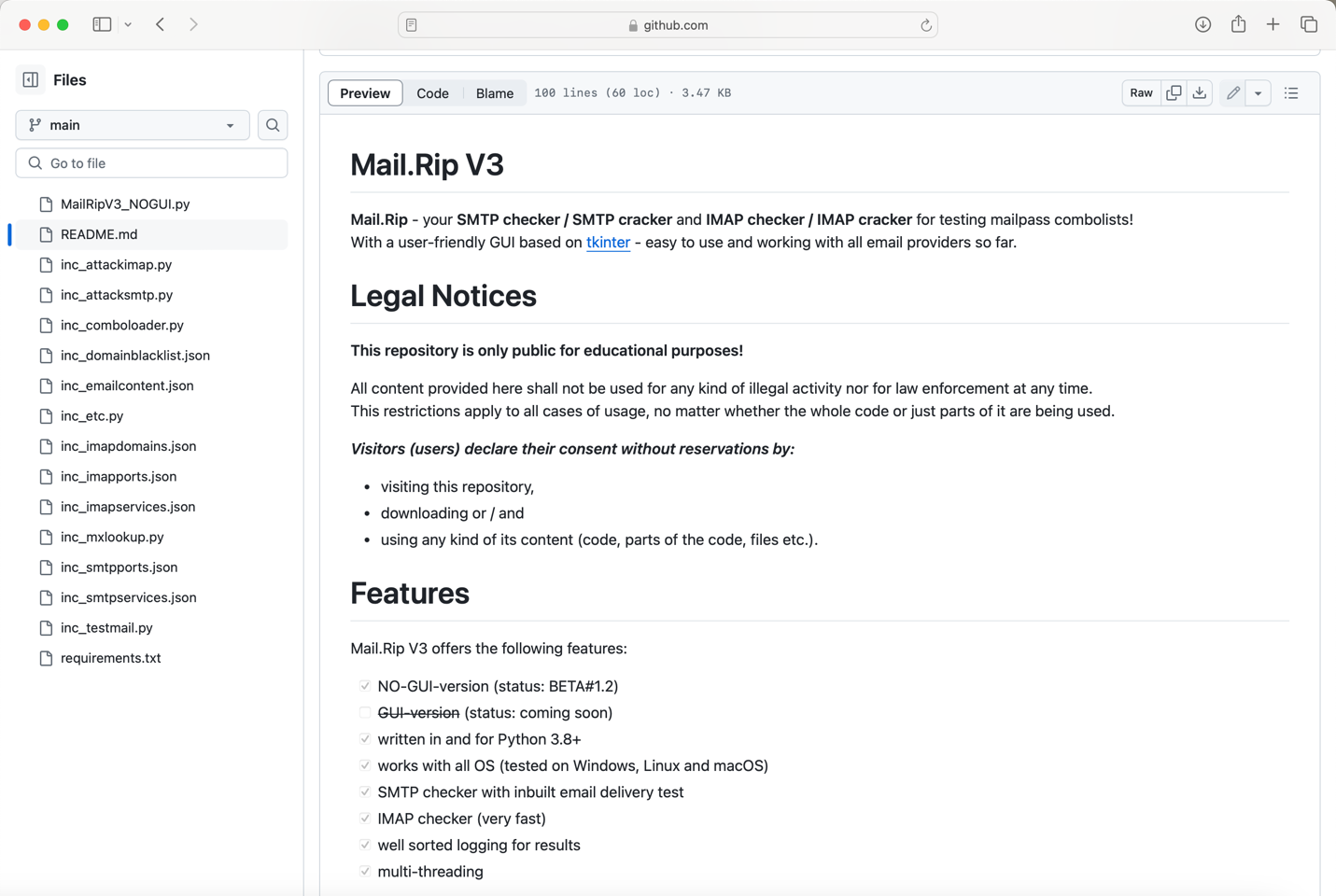
Another tool that Talos frequently sees performing credential stuffing is a program named MailRip. Although it contains a disclaimer that the code is not to be used “for any kind of illegal activity,” it is a tool primarily designed to facilitate checking username/password combos on IMAP servers and outbound SMTP servers.
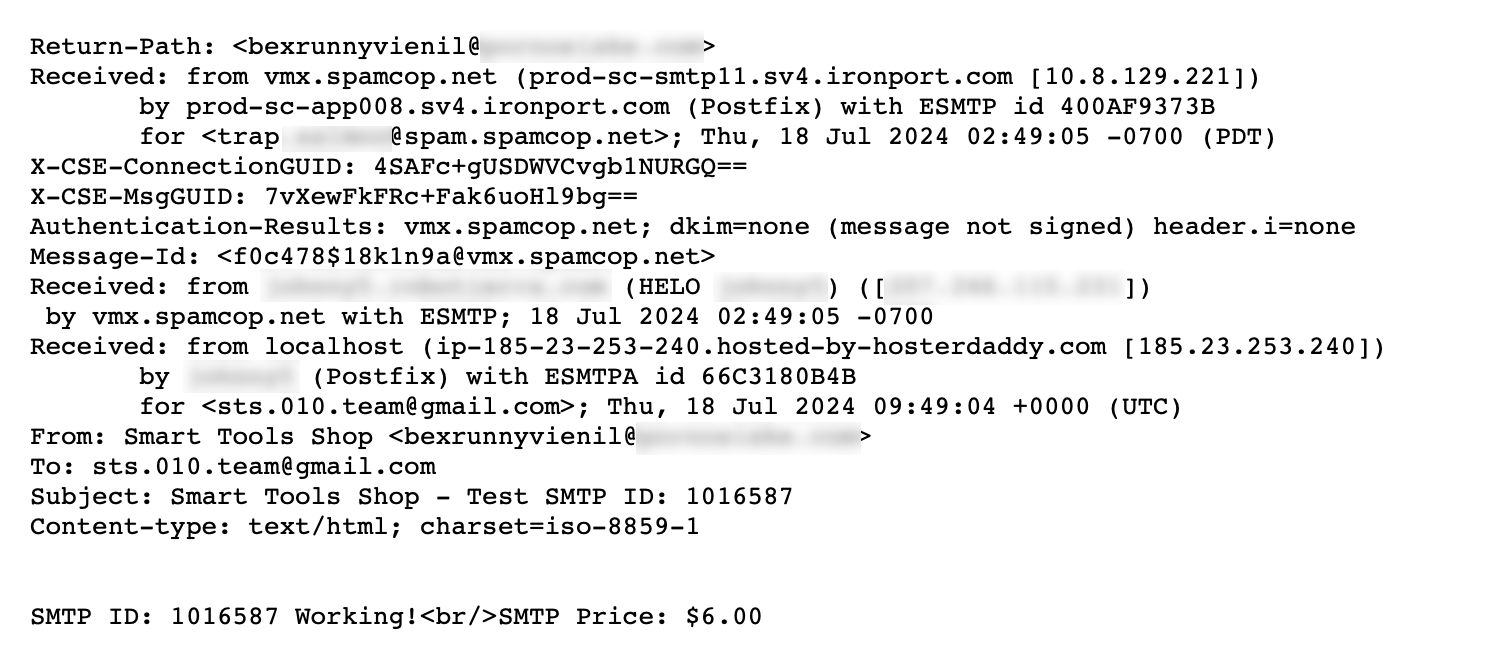
Besides these commercial and open-source tools, Talos also sees attackers who have “rolled their own” tools used for this activity. Typically, the Subject headers are a giveaway that the messages are test emails looking for valid SMTP accounts. However, some of the subject headers and email bodies of test messages are encoded/encrypted. Below are some of the more frequent Subject headers Talos has encountered.
Common Credential Stuffing Test Message Subject headers:
Subject: Mail Inbox Test IDF50F22
Subject: You get a new smtp (from MadCat SMTP cracker tool)
Subject: smtp id 2496130
Subject: g1ukczr0iz3b6o6xsk0al0tyqy8ggr (encrypted/encoded Subject/Body)
Subject: test
Subject: Testing: mx.example.com
Subject: new SMTP from MadCat checker
Subject: Smart Tools Shop - Test SMTP ID: 1016587
Subject: MailRip Test Result ID0BAB7A (from MailRip Tool)
Subject: !XProad mx.example.com|2525|nywepaq@example.com|f29r21caT4. (from Laravel Monster Tool)
Subject: SMTP Check #131085 - Jemex Shop
Subject: TESTING RELAY!
Subject: SMTP Check #6148 - Spyxe Shop
Subject: Your Account ID #62363
Subject: Mail Test Result ID0CD637.
Subject: aloha: 127.0.0.255
Subject: Mail Auto-Email ID86E8A6
Subject: Mail Email Test ID23CB4D
Subject: Mail Test Result IDD762AB
Subject: =?utf-8?q?New_working_smtp_=2350131001?=
Thwarting SMTP server credential stuffers
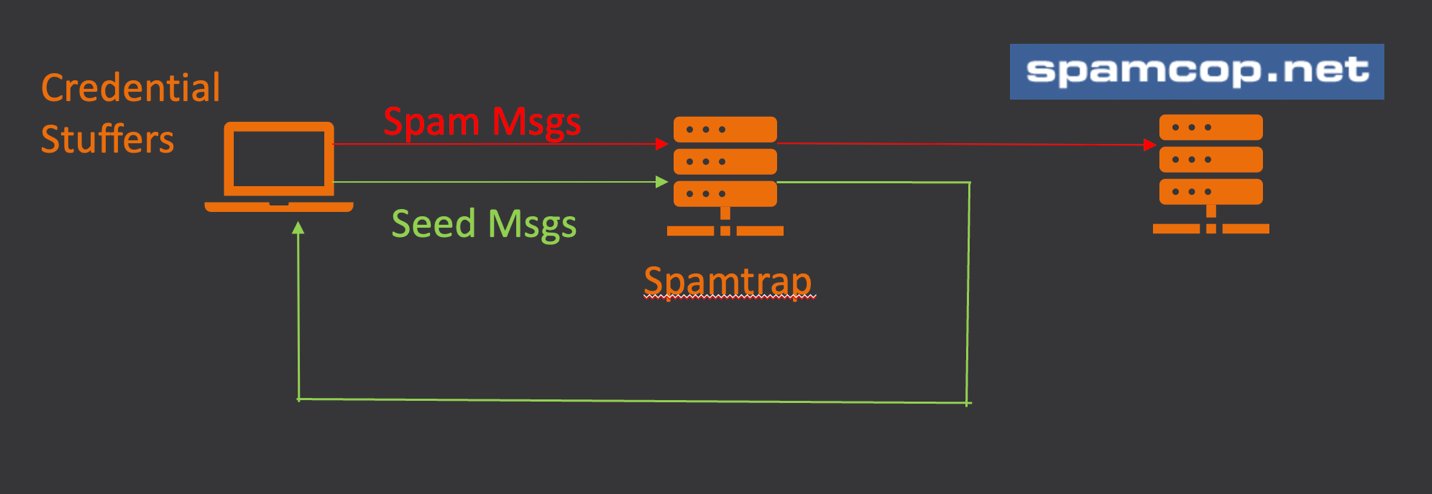
One way Talos has tried to thwart these types of attacks is to make them believe that the actors have found a working outbound email account.
To accomplish this, Talos has configured some of our spam traps to deliver those messages we have identified by Subject as test messages from the credential stuffers, while every other email is sent to various internal anti-spam systems for processing. Once the credential stuffers believe they have found a valid account, they typically turn on the spam firehose, which causes all the connecting IP addresses to be dinged for sending spam, which significantly affects those addresses' ability to deliver mail to the inbox.
The anti-spam industry has largely been successful at driving a wedge between legitimate senders and spammers, causing spammers to seek out new ways to deliver their mail.
Rather than send directly, these spammers have chosen to try and blend in with legitimate traffic to make their spam more difficult to block.
Defenses
Create Unique Passwords: People are terrible at creating and remembering good passwords. For the past several decades, even, the most popular unsafe password has been “123456”. Despite years of guidance from the security community that people should use a unique password for every website, many users will re-use the same credentials at several different sites. When someone is using unique credentials everywhere, one single compromised account will not impact any other online accounts belonging to that victim.
Use a password manager: All those unique passwords you have been creating are going to be hard to remember. But avoid storing credentials in a browser. These can be stolen by attackers quite easily. A perfect tool exists for storing your passwords: a password manager. It is best to use a dedicated password manger such as KeePass, LastPass or 1Password.
Educate Users: Unfortunately for defenders, there is very little we can do to defend against spam messages sent from legitimate forms. Most of the emails sent via forms are legitimate, so the malicious email blends in with the otherwise legitimate email traffic. However, on the positive side, some of the extra content in the emails gives away that the message is not legitimate. Educating your users to be wary of such email messages is a good way to prevent them from falling victim to phishing and other attacks that arrive by email.
from Cisco Talos Blog https://ift.tt/VwRrjbB
via IFTTT
No comments:
Post a Comment